This article was originally published on Undark. Read the original article.
In late 2020, a large box arrived at Juan Gilbert’s office at the University of Florida. The computer science professor had been looking for this kind of product for months. Previous orders had yielded poor results. This time, though, he was optimistic.
Gilbert drove the package home. Inside was a transparent box, built by a French company and equipped with a 27-inch touch screen. Almost immediately, Gilbert began modifying it. He put a printer inside and connected the device to Prime III, the voting system he has been building since the first term of the George W. Bush administration.
After 19 years of building, tinkering, and testing, he told Undark this spring, he had finally invented “the most secure voting technology ever created.”
Gilbert didn’t just want to publish a paper outlining his findings. He wanted the election security community to recognize what he’d accomplished—to acknowledge that this was, in fact, a breakthrough. In the spring of 2022, he emailed several of the most respected and vocal critics of voting technology, including Andrew Appel, a computer scientist at Princeton University. He issued a simple challenge: Hack my machine.
Their access would be unfettered—no tamper-evident seals to avoid, chain-of-custody procedures to subvert, or mock poll workers to dupe—and they’d have to agree to only one condition: Flip every vote to the same candidate.
By this point, Gilbert had published a video of his ballot-marking device, or BMD, in action, but he was unsure how the hacking community would respond. “There’s a part of that community that’s very confident in what they do,” he said. “And if they hear how it works, they may run away from it.”
After nearly two decades in the election space, Gilbert knew he was jumping feet-first into perhaps the most contentious debate over election administration in the United States—what role, if any, touch-screen ballot-marking devices should play in the voting process. Federal law requires polling sites to have at least one voting machine on-site that can serve voters with disabilities, and at least 30% of votes were cast on some kind of machine in the 2020 general election, as opposed a hand-marked ballot.

Advocates say the electronic voting systems can be relatively secure, improve accessibility, and simplify voting and vote tallying. Meanwhile, academic critics like Appel have argued that they are insecure and should be used as infrequently as possible. Those arguments have at times been bolstered by a rich, informal community of hackers who spend their time proving that they can hack the devices.
Recently, this formerly niche debate has been embraced by a chorus of conspiracy theorists who claim, with no evidence, that compromised machines cost Donald Trump the presidency.
Amid these concerns about election technology, a handful of innovators—including Gilbert—have searched for a solution that will silence critics: a voting machine that’s easy to use, based in open-source software, and significantly more difficult to hack than existing models. But some experts believe that the pursuit is misguided, because no computer could ever be unhackable. And even if Gilbert’s machine were foolproof, he and others argue that vote hacker culture—one that’s more intent on destroying devices than creating them—makes it unlikely the machine would ever get a fair hearing, let alone be adopted.
For two decades, the rise of voting technology has enabled some of the United States’ loftiest democratic ideals, and also embodied its most visceral political suspicions.
Gilbert believes he’s invented his way out of that dilemma. Who will prove him wrong?
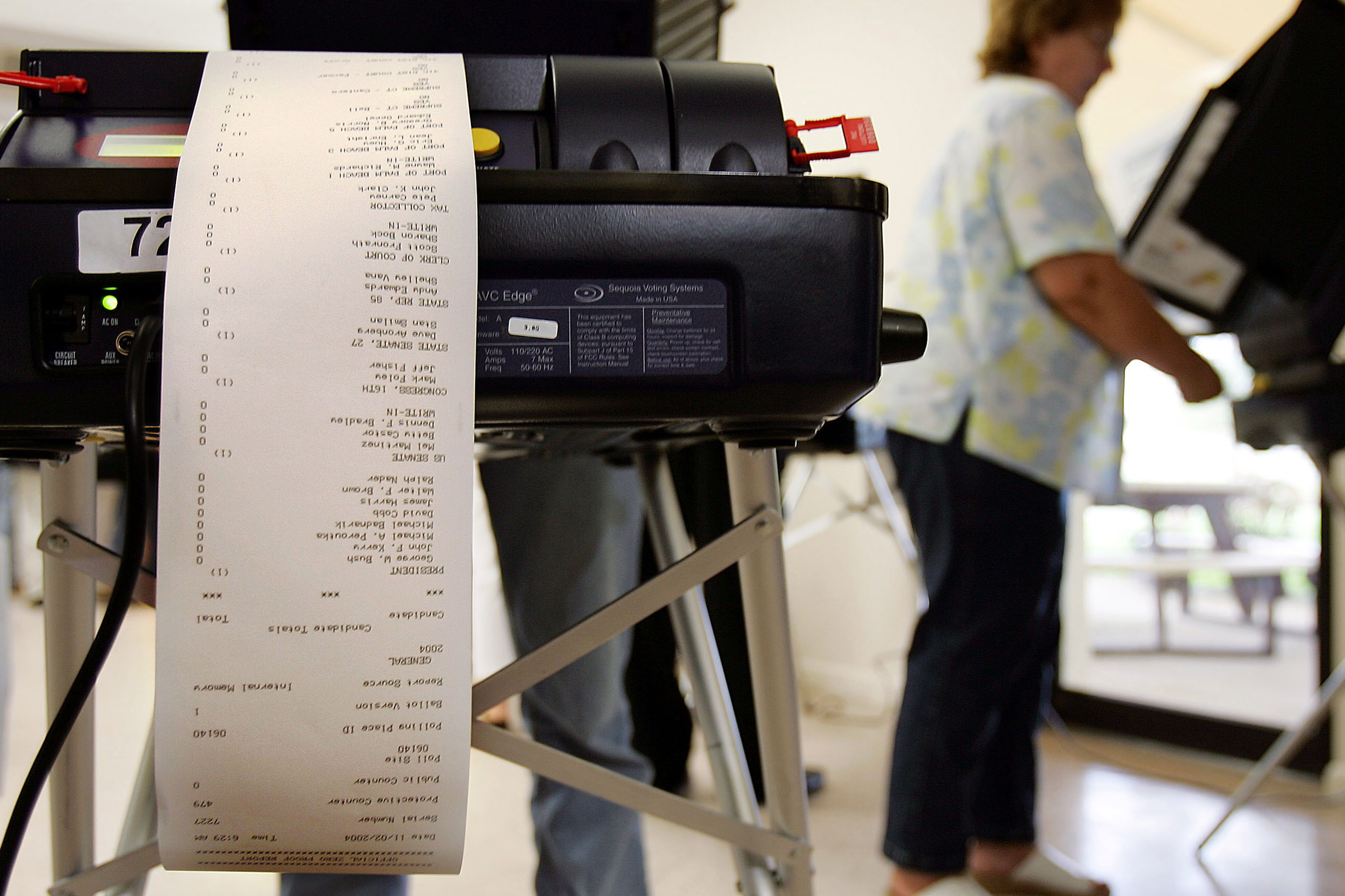
Today, the voting machine market is dominated by three major vendors: Election Systems & Software, Dominion Voting Systems, and Hart InterCivic. According to one estimate, the entire industry generates approximately $300 million in revenue annually.
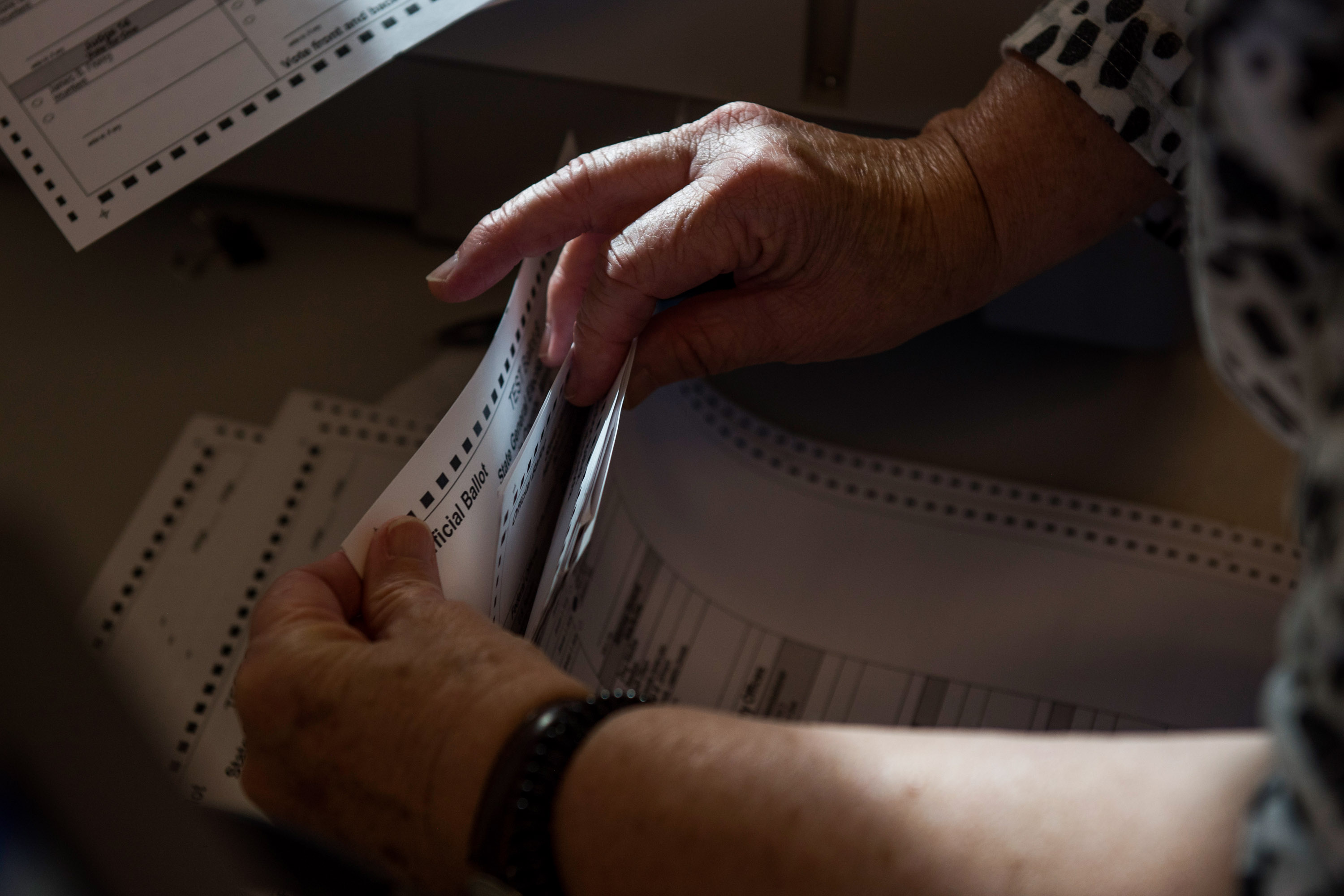
In much of the country, when somebody votes, they just fill out a paper ballot, which is typically fed through a tallying device called an optical scanner. Elsewhere, some voters use fully digital setups, called direct recording electronic systems, that sometimes use the computer to both mark and tally the votes.
A ballot-marking device has elements of both kinds of systems. While specific designs vary, BMDs have a computer touch screen for voters to make their selections. The machine then prints out a paper ballot that can be fed into a scanner. Unlike hand-marked paper ballots, BMDs have the ability to accommodate every voter using a variety of accessibility devices—including voters who can’t see, handle paper, or even touch a screen.
The machines have proliferated since 2002, when Congress passed the Help America Vote Act.
Among other momentous changes, HAVA phased out punch-card systems, like the one that produced the infamous “hanging chads” in Florida in 2000, and allocated roughly $3 billion to states, part of which was used to buy new machines—whether they wanted to or not. As a requirement of the bill, every polling site in the country must have at least one machine for people with disabilities.
The importance of HAVA to the disability vote “can’t be overstated,” says Michelle Bishop, voter access and engagement manager for the National Disability Rights Network, the nation’s largest provider of legal advocacy services for people with disabilities. Prior to the law, she says, “we had just sort of been living with systems that essentially disenfranchised large numbers of voters.”
Machines have other advantages over paper ballots: they can offer multiple language options, support larger jurisdictions that need thousands of different ballot types, and ensure that voters don’t inadvertently miss a race or make a mistake that disqualifies their ballot. Those errors can sometimes have a decisive effect: in 2008, for example, the margin of victory in Minnesota’s Senate race was well below the number of ballots rejected for voter error.
But mechanized voting brings its own set of fears, too—in particular, that someone could tamper with the machines and manipulate the results. And, some experts say, the companies’ behavior has done little to inspire public trust. “They’ve generally done things the way I would say a ’90s IT firm would do things,” said Ben Adida, the executive director of VotingWorks, a nonprofit that has developed its own open-source voting machine. “Very secretive, don’t talk to the press much, definitely don’t talk to researchers, curl up into a ball every time there’s a security report and deny, deny, deny.” (The companies tell the story differently—saying that protecting their source code, audit logs, and parts of the machines’ operating manuals is a necessary security protocol, especially now.)
Over the past two years, questioning the security of our voting machines has become its own political movement.
In York County, Pennsylvania, residents attempted to get an initiative on the November ballot that would remove the area’s electronic voting machines. In Arizona, Kansas, Michigan, New Hampshire, and Oregon, there are pending lawsuits challenging the reliability of electronic voting machines, and a special prosecutor in Michigan will investigate whether the Republican candidate for attorney general illegally gained access to voting machines after the 2020 election to perform “tests.”
These advocates offer little proof that the machines have been hacked.
However, there is a legitimate concern that they could be, say computer scientists like Appel, the Princeton professor. An expert in programming languages and computer security, Appel has publicly questioned voting technology for years. In one 2009 appearance before a court in New Jersey, he installed vote-stealing software in a machine in just seven minutes, using only a lock pick and a screwdriver.
Appel and other computer scientists fear that a hacker could slip malicious code onto a ballot-marking device—changing votes, sowing chaos, and perhaps even altering the outcome of an election.
These critics say that the code in BMDs is complex, often poorly organized, and extremely long, making it easier to insert code that goes undetected. Because the races and candidates change every election, a new ballot design must be uploaded before every contest, offering another opportunity for malicious code to slip in. And because voting is done anonymously, Appel notes, it’s impossible to link a specific ballot to the person who cast it. “There is no action a voter can take to demonstrate to election officials that a BMD altered their expressed votes,” Appel and two colleagues wrote in a 2020 paper.
In response to such concerns, voting machine companies acknowledge that their equipment may have vulnerabilities. But, they say, nearly all the machines leave a paper trail that can be audited, making it possible to catch incidents.
Still, experts say, a hack could have far-reaching effects. In September 2016, Appel submitted written testimony to a House committee hearing on election integrity. “I strongly recommend,” he wrote, “that, at a minimum, the Congress seek to ensure the elimination of ‘touchscreen’ voting machines, immediately after this November’s election.”
Juan Gilbert may seem like an unlikely candidate for a voting machine inventor. His family wasn’t particularly political growing up, he says. He doesn’t remember when he first voted.
But Gilbert loves a challenge.
During Gilbert’s junior year of college, when a professor of his suggested he become an academic himself, Gilbert thought it was a joke. At Miami University, 20 minutes from where he grew up in Hamilton, Ohio, he planned to get an undergraduate degree, find a job, and start earning a living.
“I had never seen an African-American computer science professor,” he wrote in a 2002 essay, “and so had concluded that it was not a job for me.” In 2001, he was the first African-American at the University of Cincinnati to receive a PhD in computer science.
Ever since, Gilbert has worked to diversify the field. The graduate students in his Computing for Social Good Lab are mostly women and mostly Black, and Gilbert also does outreach at organizations like UF’s chapter of the National Society of Black Engineers. At one of those meetings several years back, he met Jean Louis, then an undergraduate who had never considered graduate school. “Beforehand, I had a different view of what a computer science PhD was supposed to look like,” Louis says.
Louis now works in Gilbert’s lab, where he and other researchers are employing technology to try and solve big, ambitious problems. One piece of software they developed, Applications Quest, uses artificial intelligence to address the issue of diversity in admissions and hiring. (It’s currently used by the University of Florida for scholarship selection.) Another product, Virtual Traffic Stop, allows police officers to initiate a video call with the driver they’ve just pulled over, making the encounter safer for both parties.
“The central point is that this technology interacts with people,” says Louis of the work being conducted in Gilbert’s lab.
“It’s not just theory,” he says, “but like actually putting into practice where you can help people out.”
Louis was a coauthor with Gilbert on one of their recent papers about the BMD, and the voting machine, he said, has been a special obsession for Gilbert. “Dr. G is on another level,” Louis says. “He’s visibly, auditorily, all the ‘-lys’ passionate about Prime III.”
In the early 2000s, Gilbert says, he was at an engineering conference with his graduate students. None of them had been previously looking at voting machine design, but they were interested, especially after the 2000 election and the meltdown of Florida’s punch-card system. The students were crushed by what the speakers there had to say: “You can’t use machines. It won’t work. There’s no way to do it,” remembers Gilbert.
Now that Gilbert had heard someone say it couldn’t be done, he was fired up. In 2003, he and his team released their first prototype of Prime III. The machine allowed voters to make their selections not just by touching a screen, but also by using a headset and microphone or a paddle system, accommodating voters with physical disabilities and those who have difficulty seeing, hearing, speaking, or reading. Real-world testing led to adjustments. After there was a distracting amount of background noise during a test run at the Alabama Institute for the Deaf and Blind, he changed the system to better detect a voter’s voice. Before it was used by a group of voters with varying degrees of literacy, he added pictures to the ballot.
As Gilbert’s machine was taking shape in the early 2000s, the politics around voting technology became increasingly complicated.
In August 2003, the year before George W. Bush would win reelection, Walden O’Dell, the CEO of Diebold, wrote a letter inviting 100 friends to a Republican fundraiser at his home. In the letter, O’Dell, whose company made the machines that roughly 8% of voters used in 2000, said he was “committed to helping Ohio deliver its electoral votes to the president next year.” The letter alarmed some observers. “There are enough conflicts in this story to fill an ethics manual,” then senator Jon Corzine, a New Jersey Democrat, told the New York Times that year.
In 2007, another voting machine vendor, Smartmatic, sold its US subsidiary in order to end a months-long review by the Committee on Foreign Investment in the United States of whether the Venezuelan-owned company had ties to the Venezuelan government.
Around the same time, some computer scientists and hackers were exposing grave insecurities. In California, a team commissioned by then secretary of state Debra Bowen found a litany of problems with one of the state’s machines: viruses could jump from machine to machine and even to the election management system; a voter could delete all electronic records of the previous votes cast, even the backup copies; and the electronic and paper records had enough detail to put the secrecy of the ballot a risk.
Based on those discoveries, Bowen took the radical step of temporarily decertifying many of the state’s machines in 2007, just three months before the state’s presidential primary. “It was a scary thing, thinking about not having a system,” said Cathy Darling Allen, the county clerk for Shasta County, in Northern California.
But “in hindsight,” she said, “it was really the right thing to do.”
As hackers began to challenge voting machines, Gilbert kept developing his solution. In 2018, Prime III’s software was used in New Hampshire, after being piloted a few years prior. That year, it also debuted in Butler County, Ohio, where Gilbert grew up.
“It’s nice to see somebody who’s passionate about the work he does,” says Eric Corbin, deputy director of Butler County’s elections board. Corbin occasionally needs technical support and small tweaks to the Prime III code, so he calls or texts Gilbert. “I’d be surprised if I looked back and it took him more than 24 hours to get back to us,” Corbin says.
The latest version of the machine, which Gilbert and his students finalized this year, has all the parts of a normal voting machine: a touch screen for voters to make their selections and a printer to create a paper ballot that is then fed into a scanner.
The machine also has some more distinctive security features. The touch screen is transparent, allowing voters to watch the machine print their ballot, in real time, and notice any issues. The whole machine is also encased in fully transparent glass, making it difficult to insert, say, a malicious USB drive undetected. And the machine’s operating system, software, printer connection, and ballot information are stored on a read-only Blu-ray disc. Unlike a typical hard drive, which voting technology skeptics say could be manipulated to change a person’s votes, the disc cannot be overwritten, modified, or changed in any way. “I have taken away that ability,” said Gilbert. “You cannot change it.”
To further ensure that the USB ports can’t be used to upload mischievous code, Gilbert’s machine reboots after every cast vote. “That caveat blows out a whole lot of their issues,” he says. “No software can persist, right?”
Like most BMDs today, the machine also produces a paper ballot that can be audited. One long-standing concern about these paper trails is that voters don’t actually verify whether what’s printed on their ballot matches what they selected on the machine. If that’s the case, then audits are no use.
This is why Gilbert’s machine is so innovative, he says. The transparent touch screen forces voters to look directly at the paper being printed, making it far more likely that voters will notice any tampering. And if that happens, he says, the voter can raise an alarm.
By early May, Gilbert says, he had emailed about a half-dozen experts, including Appel and Harri Hursti, the cofounder and co-organizer of the Voting Machine Hacking Village at DEF CON, the annual hacking conference in Las Vegas. He’d issued his challenge: Could they hack the machine?
DEF CON, in particular, seemed like the perfect opportunity for Gilbert to showcase his BMD.
According to a 2017 report written by Hursti and several collaborators, the Voting Village was launched in 2017 “to highlight cyber vulnerabilities in US election infrastructure.” At the gathering, attendees have the tools, access, and free time to unscrew, disassemble, and essentially destroy all of the machines on-site. The event sometimes produces viral content, like a 2018 Twitter video in which hacker Rachel Tobac said she’d gained administrator access on a voting machine used in 18 states. “Requires no tools and takes under 2 minutes,” Tobac wrote on Twitter. “I’m concerned for our upcoming elections.”
Hackers there do exactly what Gilbert had been asking for—spend days tearing machines apart, free of charge—and their confidence that all BMDs are insecure rivals Gilbert’s confidence that his is not.
“We know every single machine in this room can be hacked,” Hursti said at the start of the convention in August 2021. “And every future machine can be hacked.”
In addition, DEF CON attendees habitually criticize the machine vendors for keeping their code secret. Not only is Prime III open source, but Gilbert’s BMD, with its transparent casing and automatic reboot after every vote, would present a unique challenge.
The DEF CON culture has frustrated some observers. “At some point, you have to move beyond just the constant critiquing and move on to productive solutions,” says Amber McReynolds, the former director of elections for the City and County of Denver and a current member of the Postal Service Board of Governors. Otherwise, she says, you risk having your research weaponized by people bent on discrediting the whole system. “I’d like to see the community of election security professionals be more thoughtful about the downstream impacts of their comments and their work on election officials, and also democracy as a whole.”
By September, Gilbert still hadn’t heard from Hursti. In fact, nobody had agreed to test the machine.
When Undark reached out to the experts Gilbert had originally contacted, they offered different explanations for their silence. One said that he had retired. A second was in the hospital. Hursti said that Gilbert had emailed his personal account, not the official one for DEF CON’s Voting Village. Asked whether he would include the machine in next year’s event, Hursti did not respond to repeated messages from Undark. The day before the publication of this story, he wrote to clarify that Gilbert’s machine would be welcome at next year’s convention, provided that he followed certain DEF CON policies, including that the hackers not be required to sign nondisclosure agreements.
Appel declined to test the machine, saying he didn’t have the resources to give it a thorough vetting. But he had seen the video of the device in action and heard Gilbert give a presentation on the new model. It was a good design idea, he said, and the lack of a hard drive provides fewer attack surfaces for a hacker to exploit. The device, he added, is addressing a problem with ballot-marking devices that nobody else has really tried to tackle.
Still, Appel said, he is skeptical of the very idea of unhackability. And he imagined scenarios during which, he said, Gilbert’s design might founder. In a blog post published in April of last year, for example, he wrote that the system depends a great deal on human voters’ being prompted to review their votes. A subtle hack, Appel suggested, could simply remove that prompt. “This gives the opportunity to deliberately misprint in a way that we know voters don’t detect very well,” he wrote.
Appel brought up another scenario: say that a voter tells a poll worker that the machine printed the wrong name on the ballot. Gilbert has prepared for this scenario: it’s possible to compare the master disc to the one in the machine to detect if there’s fraudulent code. Assume that the poll worker is able to execute that plan perfectly during the confusion of Election Day, and it reveals that the machine’s been tampered with. What then?
It’s unclear whether Gilbert’s machine will ever find wider use. Dan Wallach, a computer scientist at Rice University, said the machine was a promising step forward. Still, he voiced concerns about the durability of the machine’s parts. Appel pointed out that any new technology will face issues in being scaled for mass production and require training and for voters and poll workers.
There are other hurdles, too. For potential newcomers to the industry, it’s tough to break in, says Ben Hovland, a commissioner with the Election Assistance Commission, which was originally created by HAVA to enact the law’s requirements, including distributing the federal funding for machines. For starters, the industry isn’t that big. “While there are a lot of jurisdictions all over the country, there’s a fixed amount of equipment to sell,” he says.
“And if the jurisdiction recently bought equipment, they may not be looking for 10 years, maybe more.”
Most states also require machines to be certified, which the vendors must pay for. Under EAC guidelines, Gilbert could have to fork over hundreds of thousands of dollars to undergo that process.
Moving forward, Gilbert is planning to write a new paper detailing his design, and he is still hoping to find a hacker willing to test out the machine. The experience has left him sounding jaded about the world of election hacking —a world, he suggests, that often seems focused more on performatively tearing apart machines than actually working toward solutions.
“They only look at things they know they can break,” Gilbert says.
“If you have something that you can’t on the face of it figure out before you touch it, they’re not going to touch it.”
Spenser Mestel is a poll worker and independent journalist. His bylines include the New York Times, the Atlantic, the Guardian, and the Intercept.


